It’s been a while since a scam email has hit my inbox. But, I have a new one that is pretty interesting to me. Let’s start with the email in question

So this scam leverages the Norton brand to do its dirty work. That makes sense as you’re more likely to respond to a scam if it purports to be from someone whose name you recognize. But what is interesting is that there’s nothing for you to click on such as a link to a website for example. We’ll get to that part of the scam in a moment. But let’s dissect this to understand why this is a scam. You’ll note that the English in this email is really bad as evidenced by phrases like “In sympathy” and “please contact us as soon as possible to avoid the recent transaction dispute”. But there’s one other hint that this is a scam. When I check the email address, this is what I see:

Norton is owned by Broadcom which is a massive billion dollar company. Billion dollar companies don’t use Gmail. Ever. So if you see an email from a billion dollar company, or a million dollar company for that matter that uses Gmail or any public email service, it’s a scam and you should delete the email in question.
So, let’s get back to the fact that the email doesn’t have you click on any links. The clear intention the email is to get you to phone into the scammer. Presumably to get you to let some person take control of your computer to do who knows what to it. Or to gain your confidence to allow them to do something like take over your bank account. Which reminds me of this case where a client of mine almost lost a pile of money to a scam like this.
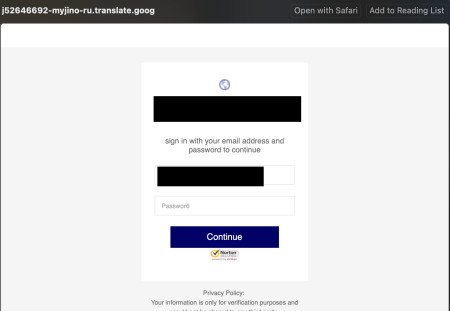
In the interest of finding out what this scam is all about, I called the number, WHICH YOU SHOULD NEVER DO, and got a very bad connection to someone who was clearly in India based on the accent. This person had me “verify” the payment number at the top of the email and put me on hold. There was actually hold music playing until he accidentally disconnected me. I called back and got the same guy which implies that this is a small operation. Though I did hear other people in the background which might imply that he was in a call centre of some sort. In any case, he then claimed that a “David from Ohio” had purchased Norton Antivirus and if I was him. When I said that I wasn’t, he claimed that someone had gotten my “financial details” and he needed to walk me through the process to cancel the software. That’s when he directed me to TeamViewer.com. I hung up at that point as I got everything that I needed. What this scammer was going to do was get access to my computer, then likely walk me to a fake website, then use that as a means to get to my bank account so that they could drain it. In other words, it is a similar scam to the one that I linked to in the paragraph above.
So, what is the take away from this? If you get an email from a company that you don’t have any services with, delete the email as falling for a scam like this never ends well.
UPDATE: A reader correctly points this out:
























BidenCash Market Posts 2Mill Credit Cards Online In Birthday Blitz
Posted in Commentary with tags Scam on March 7, 2023 by itnerdFirst reported by Cyble researchers last week, this story continues to get lot of buzz from Fox News and others this week. A web site that goes by the name of Biden Cash Market has posted 2 million credit cards online as a promotional blitz to attract customers. The site operates on both on the dark and clear web, offering credit card data for sale to the public.
The leaked information includes cardholders’ full names, card numbers, bank details, expiration dates, CVV codes, home addresses, and over 500,000 email addresses. According to D3Lab’s Head of Threat Intelligence, Andrea Draghetti, while tens of thousands the numbers are duplicates, over two million of the entries are unique.
Last fall the same BidenCash Market released a free dump of over a million credit cards in a similar promotional gimmick.
Baber Amin, COO of Veridium had this to say:
“Even the most security aware can have their credit card information compromised and made available. This can happen due to no fault of the individual.
“The data dump is not just about credit card information but contains valuable information that can be used for Identity theft. This second part should be a more serious concern, as it can lead to damage to credit score, reputation, and possibly legal issues. The damage from identity theft is long lasting.
On the financial side, the two main points of credit card compromise are:
“EMV or chip cards were supposed to stop point of sale skimming. But because all EMV cards also have a mag stripe, if someone compromises the POS terminal where users are putting in their card, they can skim the information from the magstripe bypassing chip security.
“Contactless cards aka “Touch and Pay” is thus more secure than even EMV, as the card never needs to be inserted into any device and never leaves the user.
“Magecart or online skimming is the compromise of online shopping carts and checkout process. Bad actors can inject malware into ill maintained ecommerce sites.
“Additionally, all the security offered by EMV and contactless cards is nullified, when the user voluntarily enters the CC information at checkout. Not only that, but they also enter information that can be used for Identity Theft, e.g. email address, shipping address, possibly a username and a password, etc.
These are all good tips that I hope become the norm so that scams like this become a thing of the past.
Leave a comment »